In May 2013, I was the target of an attempted entrapment. Whether it was a federal agent attempting to entrap me on a contrived material support for terrorism charge or simply an individual’s attempt to embarrass me and discredit AntiPolygraph.org remains unclear. In this post, I will provide a full public accounting of the attempt, including the raw source of communications received and the IP addresses involved.
In May 2013, I was the target of an attempted entrapment. Whether it was a federal agent attempting to entrap me on a contrived material support for terrorism charge or simply an individual’s attempt to embarrass me and discredit AntiPolygraph.org remains unclear. In this post, I will provide a full public accounting of the attempt, including the raw source of communications received and the IP addresses involved.
As background, it should be borne in mind that a federal criminal investigation into providers of information on polygraph countermeasures, dubbed “Operation Lie Busters,” has been underway since at least November 2011, when an undercover U.S. Customs and Border Protection agent, posing as a job applicant, contacted Chad Dixon of Marion, Indiana for help on passing the polygraph. In December, 2012, Dixon pleaded guilty to federal charges of wire fraud and obstruction of an agency proceeding, for which he has been sentenced to 8 months in federal prison.
Doug Williams of Norman, Oklahoma, a former police polygrapher who has been teaching people how to pass polygraph examinations for some three decades and operates the website Polygraph.com, was also the target of a sting operation and in February 2013, U.S. Customs and Border Protection executed search warrants on his home and office, seizing business records. He has been threatened with prosecution but to date has not been charged with any crime.
With this in mind, I received a most curious unsolicited communication on Saturday, 18 May 2013 from <mohammadali201333@yahoo.com>. The message was sent to my AntiPolygraph.org e-mail address <maschke@antipolygraph.org> and was titled “help help help please” (155 kb EML file.) The message body was blank, but there was a PDF attachment with a short message written in Persian, the language of Iran:

I know Persian, a fact of which the writer was evidently cognizant. Here is a translation:
Greetings and respect to you, Mr. George Maschke,
I am Mohammad Aghazadeh and have been living in Iraq for five years. I am a member of an Islamic group that seeks to restore freedom to Iraq. Because the federal police are suspicious of me, they want to do a lie detector test on me. I ask that you send me a copy of your book about the lie behind the lie so that I can use it, or that you help me in any other way. I am very grateful to you.
The book to which the message refers is The Lie Behind the Lie Detector (1 mb PDF), AntiPolygraph.org’s free e-book that, among other things, explains how to pass (or beat) a polygraph “test.” Factors that made me highly suspicious about this message include:
- Why would someone who supposedly fears the police send an unencrypted e-mail acknowledging that he’s a member of an Islamic group that is trying to change the government of Iraq?
- Why would such a person also provide his full name and how long he’s been in the country?
- To my knowledge, there aren’t any Iranian-backed Islamic groups seeking to “restore freedom to Iraq.” In fact, Iran and Iraq have good diplomatic relations.
- Why did this person ask me to send a book that is freely available on-line? Note that this message didn’t ask for a “Persian edition” of The Lie Behind the Lie Detector.
I suspected the message was a likely attempt to set me up for prosecution on charges of material support for terrorism (or something similar). It seemed highly unlikely that the message could be genuine. Nonetheless, about half an hour after receiving the message, I provided “Mohammad Aghazadeh” the same advice I would give to anyone accused of a crime who has been asked to take a polygraph test:
Dear Mr. Mohammad Aghazadeh,
Our advice to everyone under such circumstances is not to submit to the so-called “test” and to consult with a lawyer and comply with applicable laws.
George Maschke
Evidently, that response was not satisfactory, for the following day, Sunday, 19 May, about 24 hours after receipt of the first message, I received the following reply (11 kb EML file):

It reads:
Greetings and great respect, Mr. Maschke,
I am very grateful to you for your reply about the lie detector test.
I am not in circumstances where I can refrain from taking the test.
I saw your book on the Internet, but because I don’t know English, I wasn’t able to use it.
I will be very grateful to you if you would send me the Persian edition of it.
I don’t know how I will pass the test.
They have frightened me greatly. What am I to do????
I replied, “Unfortunately, said book has not been translated to Persian.” I have received no further communication from this person.
I Googled the e-mail address <mohammadali201333@yahoo.com> and found no mentions. Both e-mail messages originated from the same IP address: 159.255.160.115.
This address traces to Arbil (also spelled Erbil), Iraq, where the United States has a consulate.
I checked AntiPolygraph.org’s server access log for the IP address 159.255.160.155, and here is what I found:
9 May 2013
08:24:48 (GMT), someone at this IP address landed on AntiPolygraph.org’s publications page after a search on Google.iq (search terms unknown) using Google Chrome under Windows NT 6.1 (Windows 7).
08:24:59 lands on home page after searching Google.iq for: george maschke antipolygraph.
08:25:37 downloads The Lie Behind the Lie Detector.
10:09:15 fetches The Lie Behind the Lie Detector a second time after searching “george counter polygraph” but this time with Firefox 2.0.0.12 under Windows NT 5.1 en-US (Windows XP 32-bit).
18 May 2013
07:04:18 Lands on home page after unknown search on Google.iq using Microsoft Internet Explorer 10 under Windows NT 6.1 (Windows 7).
07:04:41 Fetches Federal Psychophysiological Detection of Deception Examiner’s Handbook.
07:05:46 Fetches The Lie Behind the Lie Detector.
07:06:27 Fetches DoDPI Law Enforcement Pre-Employment Test Examiner’s Guide.
07:06:55 Fetches DoDPI Interview and Interrogation Handbook.
07:07:29 Fetches DoDPI Numerical Evaluation Scoring System.
11:07:04 Returns to home page using Microsoft Internet Explorer 10 under Windows NT 6.1.
11:07:08 Views recent message board posts. (Note: this action suggests the visitor is familiar with the site.)
11:08:10 Does a message board search (search terms not logged by server).
11:08:25 Searches message board again.
11:08:36 Searches message board again.
11:08:48 Searches message board again.
11:09:27 Searches Google (terms unknown) and lands on message board thread, Al-Qaeda Has Read The Lie Behind the Lie Detector.
11:10:02 Gets message board thread, Al-Qaeda Documentation on Lie Detection (which is linked early in the previous thread).
Note that both of the foregoing message threads include accusations against me of disloyalty to the United States.
11:10:34 Gets document Al-Qaeda Documentation on Lie Detection.
11:10:41 Returns to message board thread, Al-Qaeda Documentation on Lie Detection.
11:30:20 Last load of any page.
The browsing behavior documented in the server log does not suggest to me an individual who doesn’t know English. Also, the use of different web browsers and operating systems suggests to me that the IP address might belong to an organization rather than an individual.
I also found a few other visits from other nearby IP addresses (first three numerical blocks of the IP addresses are the same):
On 3 May 2013 at 10:51:20, IP 159.255.160.5 landed on an image of Tyler Buttle after searching Google.iq with an iPhone for “photo+sebel+can+sex”.
On 7 May 2013 at 18:08:25, IP 159.255.160.80 searched Google.iq for unknown terms and landed on the blog post Is Patrick T. Coffey Fit to Be Screening Police Applicants? using Firefox 20 under Windows NT 5.1 (Windows XP).
Twenty-six seconds later, at 18:08:51, the same IP moved on to the blog post Polygrapher Patrick T. Coffey Threatens Lawsuit, Demands Retraction.
I can well understand why someone in Iraq might search for sexy pictures of Sibel Can, a Turkish singer. (The searcher, who misspelled “Sibel,” must have been disappointed to find a picture of Tyler Buttle instead.) But why would anyone in Iraq be interested in Patrick T. Coffey, a private polygraph examiner based in Burlingame, California?

Photograph posted by Patrick T. Coffey to Facebook on 1 May 2013. The Arabic caption under the American and Iraqi flags reads: “Together We Achieve Success”
Coffey has done contract work in the Middle East before, and I wondered whether he might have been on contract in Iraq during the relevant period. Coffey lost his contract for pre-employment polygraphs with the San Francisco Police Department in the aftermath of S.F. Weekly’s reporting about bigoted and intemperate remarks he made on AntiPolygraph.org. Coffey clearly despises me, as you’ll observe from comments he posted under the nom de guerre TheNoLieGuy4U in the message thread Al-Qaeda Has Read The Lie Behind the Lie Detector. Those comments begin at page 2 and include a demand to know whether I have “personally ever translated or assisted any person in the translation of anti-polygraph materials or literature into Arabic, Farsi [Persian], or any other language?” (As if that were some sort of a crime. In fact, I haven’t.)
I was able to confirm that Coffey was indeed in Iraq for three weeks, including the relevant period when the visits to AntiPolygraph.org were made and the e-mails were sent. I called him on the morning of 26 May to ask whether he might have enlisted the aid of a Persian-speaking colleague while in Iraq in a personal effort to test and perhaps discredit me. Coffey denied any involvement with, or indeed, any knowledge of, the e-mails. He even refused to confirm that he had been in Iraq.
Coffey did volunteer that he understands from hearsay that the Department of Defense has an “open case” about me with respect to “the countermeasure question.” His implication was that it’s a criminal case. However, I have been out of the Army reserve for nine years and am not subject to the Uniform Code of Military Justice.
So was this attempted entrapment part of the U.S. government’s Operation Lie Busters, or the intrigue of a polygraph examiner with an axe to grind, or possibly a combination of both? I don’t know, but I welcome comment from any readers who might.
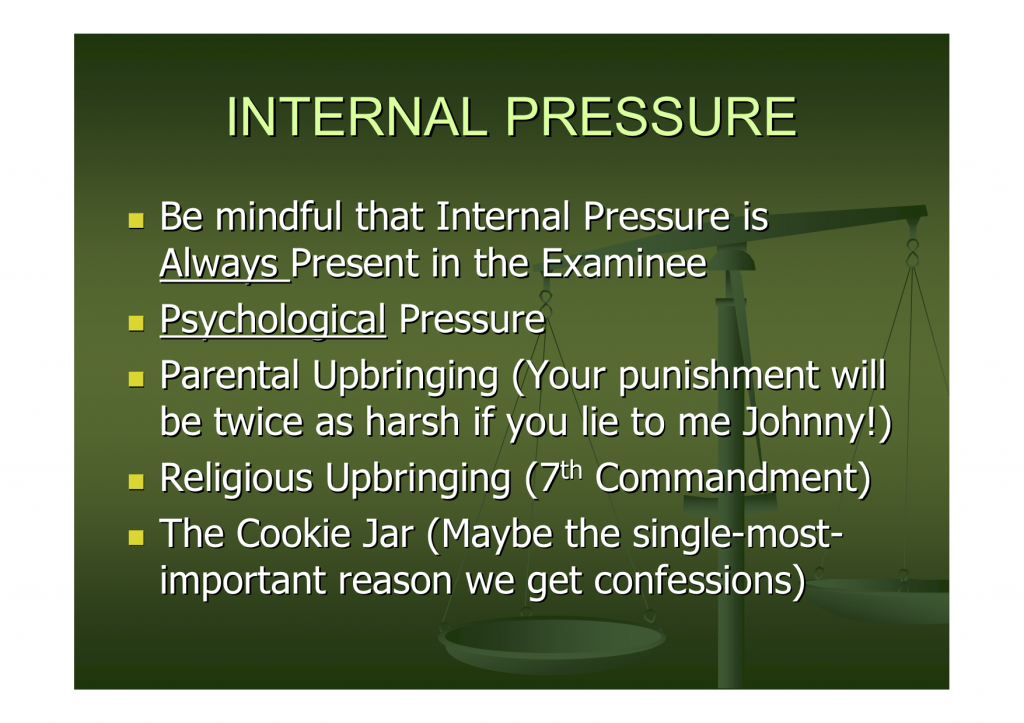 The “cookie jar” story is a simplistic tale that polygraphers like to tell during the pre-test phase. Retired FBI polygrapher Jack Trimarco explained it this way in a 2007 radio interview:
The “cookie jar” story is a simplistic tale that polygraphers like to tell during the pre-test phase. Retired FBI polygrapher Jack Trimarco explained it this way in a 2007 radio interview: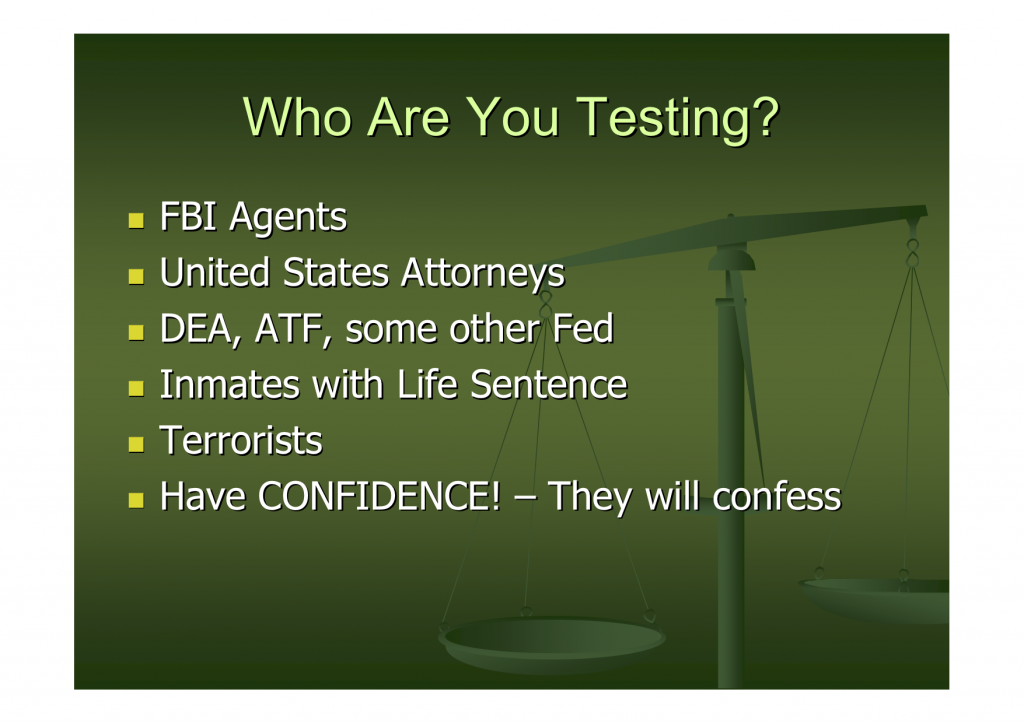
 There is an inside joke among polygraphers that they are salesmen with a difficult job: selling jail time. In slide 13, urging the polygrapher to keep the interrogation going as long as possible, Schwartz describes the job a different way: “manure salesman”:
There is an inside joke among polygraphers that they are salesmen with a difficult job: selling jail time. In slide 13, urging the polygrapher to keep the interrogation going as long as possible, Schwartz describes the job a different way: “manure salesman”: In slide 14, Schwartz specifically mentions AntiPolygraph.org, suggesting that the polygrapher should “do the unexpected” if he or she believes that the examinee has read this site (or if the polygrapher has “the feeling” that the examinee “won’t confess”). It’s not clear what “unexpected” things Schwartz advocates polygraphers doing:
In slide 14, Schwartz specifically mentions AntiPolygraph.org, suggesting that the polygrapher should “do the unexpected” if he or she believes that the examinee has read this site (or if the polygrapher has “the feeling” that the examinee “won’t confess”). It’s not clear what “unexpected” things Schwartz advocates polygraphers doing: In slides 20 and 21, Schwartz suggests a variety of polygraph techniques “if nothing else works,” including one of his own creation: “Schwartz’s Helpful Interrogation Test,” evidently an adaptation of the peak of tension test. This technique is not included in the U.S. Customs and Border Protection polygraph handbook (1.9 mb PDF), and it’s not clear if CBP polygraphers use it. Nonetheless, it is cause for concern that a federal polygrapher devised and advocated a “home brewed” polygraph technique:
In slides 20 and 21, Schwartz suggests a variety of polygraph techniques “if nothing else works,” including one of his own creation: “Schwartz’s Helpful Interrogation Test,” evidently an adaptation of the peak of tension test. This technique is not included in the U.S. Customs and Border Protection polygraph handbook (1.9 mb PDF), and it’s not clear if CBP polygraphers use it. Nonetheless, it is cause for concern that a federal polygrapher devised and advocated a “home brewed” polygraph technique:
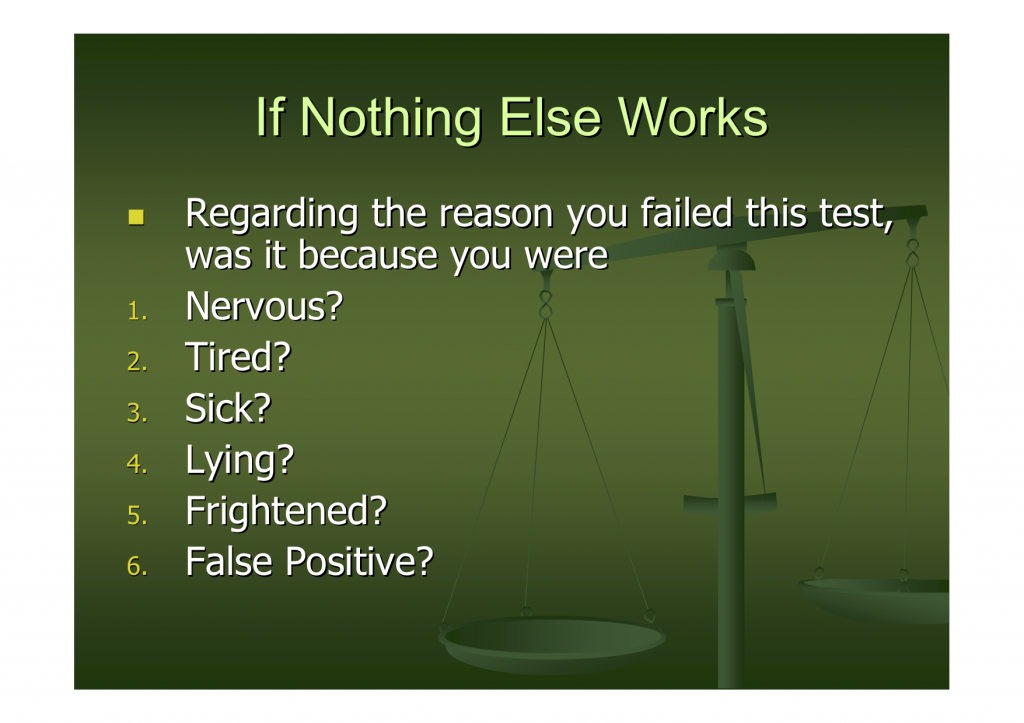 It is absurd to ask a polygraph examinee why an invalid procedure (polygraphy) may have produced an inaccurate result. It’s like asking why a coin toss came out heads instead of tails. Schwartz’s home brewed “Helpful Interrogation Test” has one thing in common with the Backster Zone Comparison Test, the Reid Modified General Question Test, and the Keeler Relevant/Irrelevant Test: it is the brainchild of an interrogator, not a scientist. Beware of manure salesmen.
It is absurd to ask a polygraph examinee why an invalid procedure (polygraphy) may have produced an inaccurate result. It’s like asking why a coin toss came out heads instead of tails. Schwartz’s home brewed “Helpful Interrogation Test” has one thing in common with the Backster Zone Comparison Test, the Reid Modified General Question Test, and the Keeler Relevant/Irrelevant Test: it is the brainchild of an interrogator, not a scientist. Beware of manure salesmen.